Github reveals how North Korean hackers create synthetic identities to infiltrate businesses

North Korean state-backed hackers are systematically building fake personas to infiltrate companies as contractors and employees, in some cases relying on a well-organized pipeline for creating synthetic identities at scale, according to a new analysis from GitHub.
The company recently shared its findings on threat actors associated with a Democratic People’s Republic of Korea (DPRK) group known as Contagious Interview. The hackers have been using the developer platform for creating malware that can steal credentials and remotely control devices, enabling financial and identity theft. They have also developed software to evade sanctions and generate revenue through IT worker schemes.
“We banned 131 accounts associated with North Korean nation-state malware distribution in 2025,” GitHub said in a blog post published last week.
In one case, the company identified a North Korean nation-state software development team that created at least 135 synthetic identities. The group scraped images and personal data, generated fake passports and automated email and professional networking accounts to generate leads.
“The threat actor developed a complex multistage process to generate synthetic identities at scale,” notes GitHub.
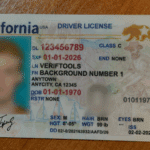
The process included scraping photographs from social media, AI image generators and other platforms, after which new facial images were generated through a legitimate tool called faceswapper.ai. They then used these headshots to create passports containing fake personal information through an illegal, fraudulent identity document service called VerifTools.
The synthetic identities, which purported to originate from Eastern Europe and Southeast Asia, were used to create accounts on email and professional networking sites. The fake passports helped verify their identities on such sites.
“For each account, the threat actor stored information about whether identity verification was successful, with overall results indicating the threat actor was successful in just over 40 percent of verification attempts,” the analysis notes.
Overall, the fake identities were used to gain access to at least 48 private codebases. The development team was most active from late 2024 to mid-2025.
Another case study described an individual North Korean operator controlling at least 21 distinct personas across five countries based on real identities. The personas were supported by fake IDs and personal information gathered from open sources and cyber intrusions and used to earn money through contract and freelance software development.
Other threat actors operate in cells, with one such IT worker cell earning US$1.64 million between the first quarter of 2022 and the third quarter of 2025.
“Identity development is a fundamental element of North Korean nation-state insider activity,” says Github. “North Korean nation-state threat actors incrementally build legitimacy through identities spanning multiple platforms and by seeking enhanced verification services where possible.”
DPRK nation-state malware operations are atypical due to the significant direct human effort involved, GitHub says. The hackers create interactions, reviews and testimonials between personas.
“The volume of manual effort by many operators presents a challenge to service providers because of the extreme diversity in techniques that emerges,” the analysis adds.
North Korean nation-state threat actors have posed as recruiters to induce software developers to execute malicious code projects under the pretense of technical interviews since at least 2022.
Malware activity accelerated in the second half of 2025 and peaked in September, while GitHub expects that the malware campaigns will continue through 2026. The company shared more than 600 indicators of compromise associated with these case studies.
How companies defend themselves from North Korean threat actors
While GitHub shared a breakdown of how North Korean IT workers operate, voice biometrics company Pindrop is showing what companies can do to prevent the unintentional hiring of threat actors.
The U.S.-based firm develops deepfake-detection technology for audio and video that can catch impostors during business meetings.
Last year, the company published an analysis of remote hiring, determining that one in six applicants shows clear signs of fraud, while one in 343 is linked to North Korea. A quarter of those DPRK-linked applicants have used deepfake technology during live interviews.
However, AI-generated media represent only a small percentage of overall impersonation activity. Most confirmed fraud cases are detected by analyzing telemetry data, including devices, geographic location, email patterns, as well as other types of signals, Pindrop notes in its blog post.
One such pattern is using older versions of operating systems, such as Windows 10 or macOS 13+.
“The complete absence of modern systems across confirmed cases is consistent with centralized device pools, reused hardware, or virtualized environments rather than independently maintained personal machines,” the company says.
The company, which predominantly helps hire in the U.S., has also found that over 40 percent of confirmed fraudulent applicants connected from non-U.S. IP addresses. Certain VPN services also trigger more scrutiny.
GitLab’s analysis showed that the vast majority of threat actors, roughly 90 percent, used Gmail email addresses. The same figures were also recorded by Pindrop.
Once a job applicant is found to be a fraud, the company extracts data and compares it with historical applicant data. In one case, one confirmed fraud led to the discovery of 23 additional suspicious applicants.
Suspicions are usually raised after analysis unearths identical resumes with different names, reused or swapped GitHub repositories, overlapping phone numbers and email structures and unknown employers appearing repeatedly.
“The connections were not obvious during resume review. They emerged only after graph expansion,” says Pindrop.
Other companies apply different tools to detect fraudulent applicants. Automated reference-checking platform RefAssured has announced a joint product this month with digital identity verification company ID.me, which allows staffing agencies to perform reference checks and identity verification before the job-seeker applies for a position.
Article Topics
AI fraud | biometrics | deepfake detection | GitHub | ID.me | identity theft | identity verification | North Korea | Pindrop | remote identity proofing | synthetic identity fraud






Comments