Twitter wouldn’t be hacked with decentralized identity platforms

This is a guest post by Katie Lu, business development associate at Unum ID.
In the afternoon of Wednesday, July 15th, Twitter fell victim to a “coordinated social engineering attack”, responsible for almost 98% of all cyber attacks. The attack affected approximately 130 high-profile accounts, including those belonging to Barack Obama, Elon Musk, Bill Gates, and Kanye West in an attempt to gain bitcoin (BTC). The tweets sent out were nearly identical and promised followers a doubling of their coin, reading along the lines of “I’ll double any BTC payment sent to this address”.
Apart from high-profile people, the hackers were also able to access company accounts such as Apple, Uber and CashApp with a similar scheme.
While a high-attention breach, not exactly surprising
However, while this particular attack garnered widespread media attention, it is only the latest in a long line of social engineering breaches. This wasn’t even the first time that Twitter has been targeted, as in August of 2019, CEO Jack Dorsey was a victim of SIM swapping, another type of social engineering where a phone number is routed to a different device. Dorsey lost control of both his mobile number and Twitter handle because hackers were able to use information such as his mobile carrier and personal information to gain access. Twitter’s not alone either — Barbara Corcoran was also victim to social engineering when an individual impersonated her bookkeeper in a $400,000 wire fraud scheme. The common thread with social engineering tactics is that a centralized organization or company has access to personal data and accounts. With Twitter, inside tools used by employees were accessed, while SIM swapping relies on a person on the inside switching numbers. Corcoran’s scheme predicated on a bookkeeper being convinced to grant access to her accounts.
The fundamental problem
The social engineering problem is a well-known, yet difficult and unsolved problem. The inherent problem is that centralized structures will always be vulnerable to attacks, with no fault from the end user. With all of these cybersecurity incidents, the response has been to boost security on existing centralized infrastructures. The problem with this, however, is that it essentially becomes an arms race. While security becomes stronger, so do hackers, making it an infinite loop of data breaches and developing more robust security.
In comes decentralized identity
Decentralized identity is a solution that has been discussed by companies such as Microsoft and others because it would solve the problem of lots of access being contained in one tool or place. In a decentralized system, each person has sole access to their own data and services only require one verification — yourself.
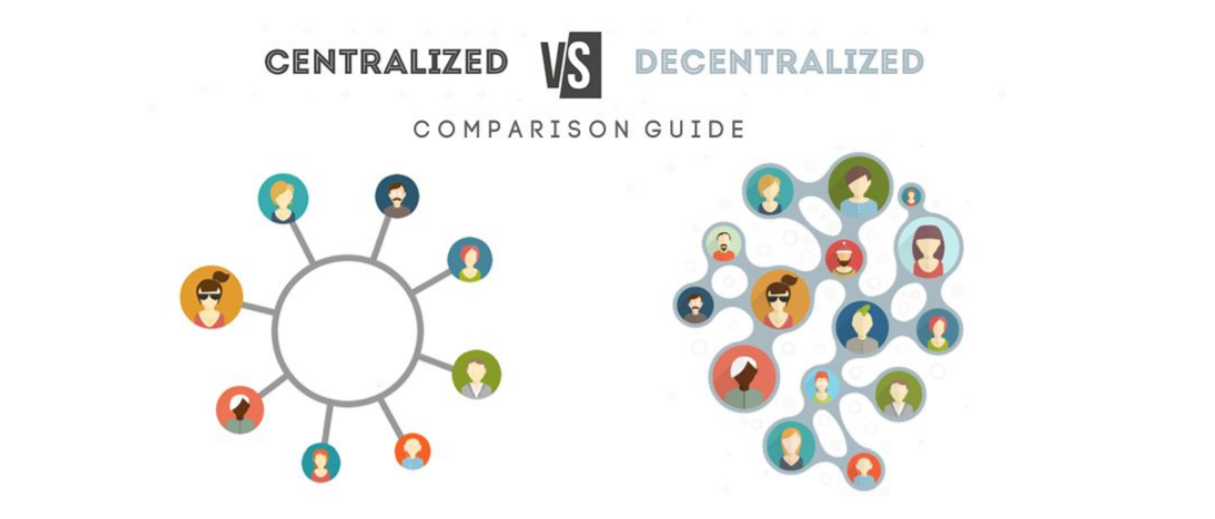
You can see in the picture above that centralized (left) allow access to everybody if the central platform is compromised; while with decentralized (right), only a single person can be accessed per breach
In our current system, you have to register separately with each service you use and re-authenticate yourself each time you log in, either with username/password or other credentials. This has many vulnerabilities, including a centralized database with your information that could be leaked, as well as the employees being able to manipulate, use, and store your data. Under a decentralized, blockchain platform, your digital data and accounts are not stored in a centralized database, they are stored on your personal device. This means that hackers would not be able to access your data unless they had your physical device, such as a phone, making data breaches significantly more difficult to do and wide-scale ones near impossible. Let’s go through a use case and see how hacks like Twitter’s would’ve been impossible with a (mostly) decentralized platform.
Johnny wants to log in to Twitter.
1. He goes to their login page and enters his usual username and password, which are already in Twitter’s centralized database.
2. He goes through verification, showing that he is indeed a person that matches the information he entered. Once this verification is done, that verification credential is stored inside of his phone as well.
3. Next time Johnny wants to log in, he uses his biometrics to unlock the correct credentials on his device and log in. Keep in mind that Twitter also proves their identity back to Johnny by authenticating with his username/password that only they would have access to. It’s that easy!
How social engineering is neutralized by decentralization
Let’s now go through common social engineering tactics, including Twitter’s case and discuss why they wouldn’t work.
1. Twitter’s case- insider employees tools used: There are two reasons why this approach would not have worked. First, in order to access the employee’s account, the only way to log in would be to have their physical device (for the login information). Secondly, the hacker would also have to have the employee’s physical person there for biometrics to release the verification credential. This scenario is very improbable and means the hackers wouldn’t have access to the employee tools in the first place.
2. SIM swapping: Because a person’s digital identity is tied to their physical device, routing the person’s phone number to another device effectively does nothing. The hacker’s device with the person’s mobile number, still doesn’t have the verification credential nor personal data to authenticate with Twitter. SIM swapping doesn’t give account access.
3. Phishing: Employees and users both, even if convinced with a fake Twitter website, couldn’t give account access because the fake site wouldn’t be able to prove themselves back. With decentralized infrastructure, the fake site wouldn’t be able to pass the username/password check to authenticate themselves to the user. Decentralization protects the users from phishing as well.
Closing thoughts
It’s clear that cybersecurity is only growing, with some reports predicting that spending would exceed $1 trillion by 2021. But as long as we continue to fight an unnecessary arms race against hackers with centralized systems, we miss a critical opportunity to inherently improve identity management systems. The most vulnerable point of access, people themselves, should be neutralized by requiring an additional check, such as their personal device and biometrics. The next generation of cybersecurity needs to focus on transitioning to a decentralized platform, helping both users and companies protect their data.
About the author
Katie Lu is a business development associate at Unum ID.
DISCLAIMER: Biometric Update’s Industry Insights are submitted content. The views expressed in this post are that of the author, and don’t necessarily reflect the views of Biometric Update.
Article Topics
authentication | biometrics | blockchain | cybersecurity | data protection | decentralized ID | digital identity | hacking | identity management | identity verification | Unum ID | X (twitter)


Comments