Verkada hack shows cameras with face biometrics capabilities deployed by thousands of organizations
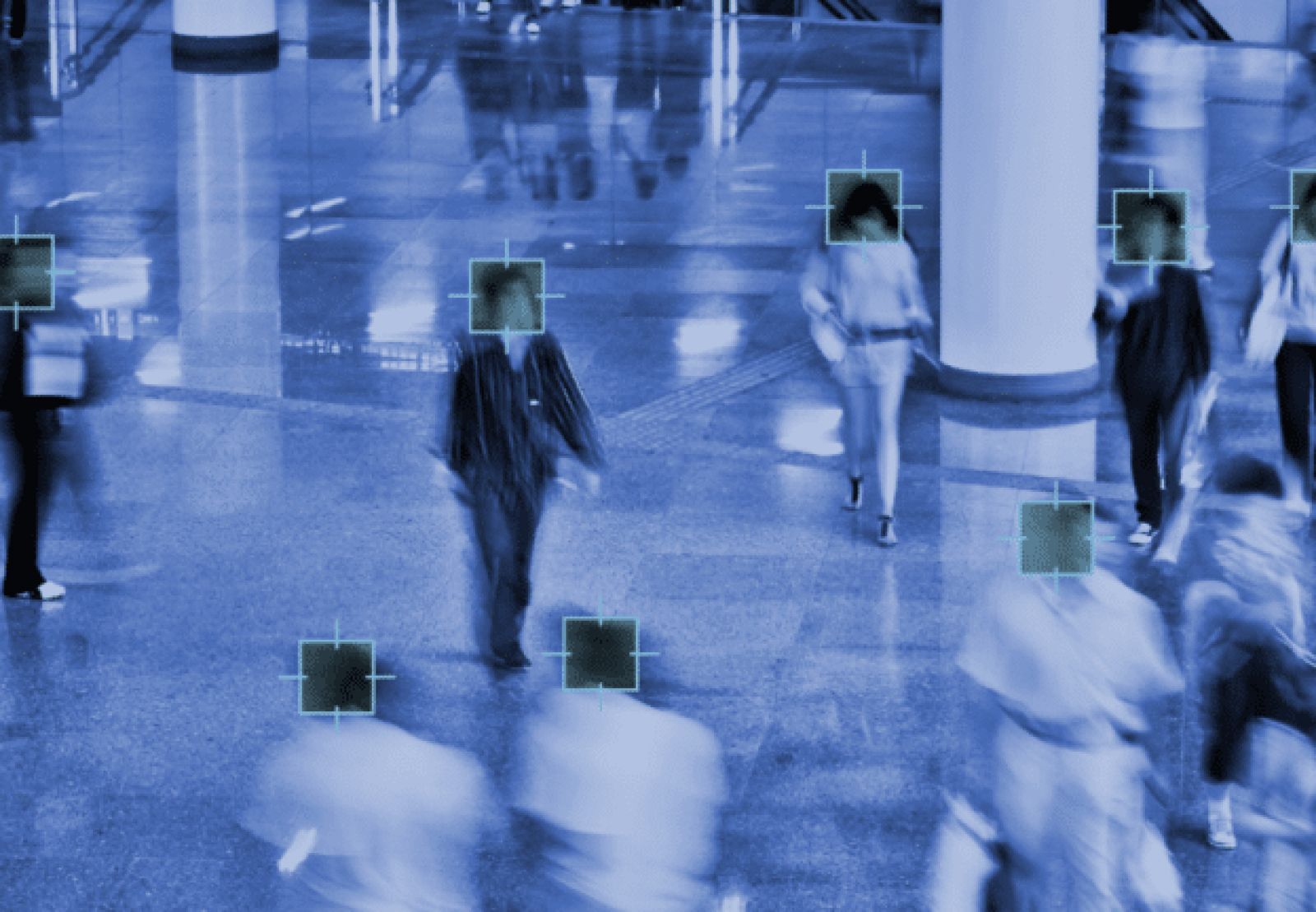
A hack of Verkada that included access to thousands of live surveillance camera feeds has revealed the widespread availability, if not use, of face biometrics in workplaces, bars, parking lots, K-12 schools, prisons and hospitals, Vice Motherboard reports.
A spreadsheet of customers with some 24,000 unique “organization name” entries was acquired by the hackers, along with access to 150,000 live feeds at Tesla, Cloudflare, police departments, jails and hospitals, according to Bloomberg.
The Verkada cameras supplying those feeds all come with edge AI and facial recognition as a basic capability, rather than an add-on, though the customer list does not indicate who is using the feature.
Organizations using the cameras equipped with biometric functionality also include universities in the U.S. and Canada, the Professional Golfers Association, churches, and airports.
A hacker named Tillie Kottman is among those claiming responsibility. Kottman told Motherboard that the group discovered a username and password online, which made accessing the cameras easy. The hack was intended to expose the prevalence of the surveillance cameras, as well as their vulnerability, The Verge writes.
Verkada told Motherboard it had disabled its internal administrator accounts to prevent continued access and put internal security and an external security firm on the case. The company also contacted law enforcement.
The company was also the subject of reporting by Vice on a less-than-professional workplace culture, which the company says it has since taken steps to address.
Article Topics
biometric identification | biometrics | data protection | edge cameras | facial recognition | privacy | Verkada | video surveillance

Comments