Singapore moves to end use of NRIC numbers for authentication
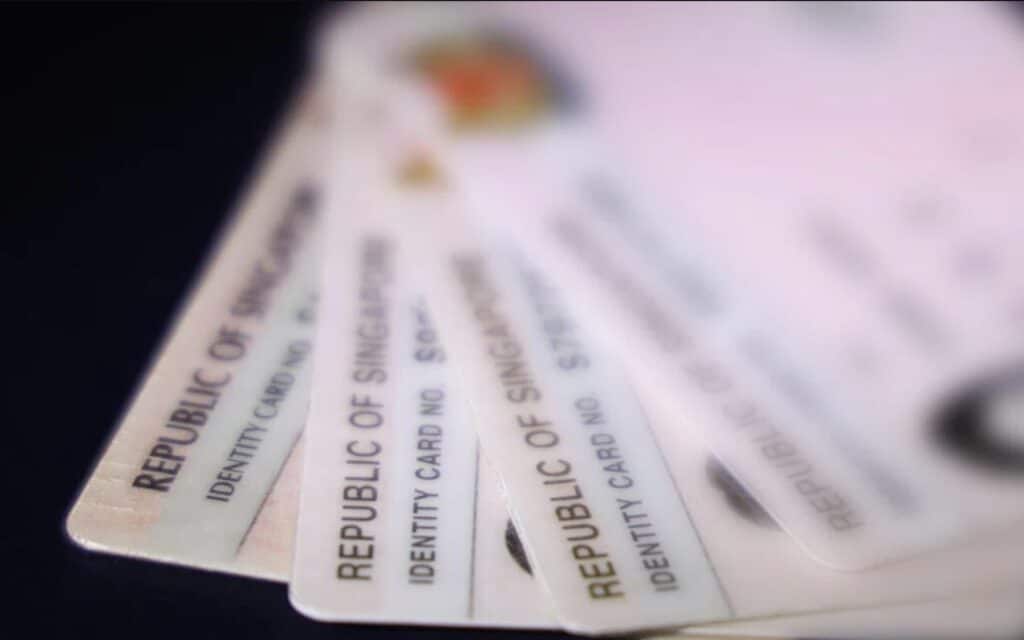
Singapore is looking to phase out the use of its National Registration Identity Card (NRIC) numbers, an official identity document, as an authentication method.
The country is giving private organizations until 31 December 2026 to stop using NRIC numbers as an authentication method. Regulators will tighten enforcement from 1 January 2027.
The Personal Data Protection Commission (PDPC) said companies that continue relying on full or partial NRIC numbers to verify identities could face directions or financial penalties for breaching the Personal Data Protection Act (PDPA).
The shift follows a June 2025 advisory from the PDPC and the Cyber Security Agency of Singapore (CSA), which warned that NRIC numbers should not be used as passwords or combined with easily guessed personal information such as names or birthdates.
Regulators highlighted examples like using an NRIC number on its own or as part of a default password, noting that such practices expose individuals to unauthorized access of accounts and digital documents. Government agencies have already stopped using NRIC numbers for authentication, and sector regulators have issued similar guidance.
The Infocomm Media Development Authority (IMDA) has advised telcos to end the practice, the Monetary Authority of Singapore (MAS) has done the same for financial institutions and insurers, and the Ministry of Health (MOH) has instructed healthcare providers to adopt alternative verification methods.
Private organizations are now expected to review their systems and remove NRIC‑based authentication by the end of 2026. The PDPC said that continuing to use NRIC numbers to access personal data may amount to failing to make reasonable security arrangements, a key requirement under the PDPA.
Updated guidance on protecting personal data, including NRIC numbers, has been published to help organizations comply.
Fixed-state identity numbers pose security risks, argues Ping Identity director
Writing in The Business Times, Johan Fantenberg, a director at Ping Identity, makes the case for why NRIC numbers make poor security credentials. The issue is that they’re fixed, widely reused and easily exploited once exposed. Their use across banks, telecoms, healthcare and government-linked services means that a single leak can enable impersonation and fraud across multiple sectors, he argues.
NRICs are often treated as proof of identity making them an attractive target for criminals, who can use stolen numbers to social engineer call center agents, bypass verification checks or escalate access on online platforms. Unlike passwords, NRICs cannot be changed, so any breach leads to a permanent vulnerability.
There have been major incidents in recent years. A SingHealth cyberattack compromised the data of 1.5 million patients; an IT error at the Council of Estate Agencies sent NRIC details of more than 3,000 people to unintended recipients; and a leak from ACRA’s Bizfile portal exposed full NRIC numbers of business owners and company directors.
To reduce these risks, organizations are encouraged to adopt modern digital identity and identity access management (IAM) systems. These include risk‑based authentication that adapts to threat levels, continuous identity verification beyond the initial login, and privacy‑preserving biometric methods such as zero‑knowledge biometrics.
Strengthening fraud‑prevention measures and being transparent with customers helps rebuild trust as worries about AI‑driven impersonation and deepfakes rise. Moving away from NRIC‑based authentication is a compliance requirement and an opportunity to shift to more resilient, flexible identity systems, Fantenberg believes. Organizations that treat identity as a core security layer will be better positioned to maintain trust and adapt to emerging threats.
Article Topics
authentication | identity document | National Registration Identity Card | Personal Data Protection Commission (PDPC) | Singapore







Comments