New NIST guidelines look at face morph attacks and how to stop them
The National Institute of Standards and Technology (NIST) has released guidelines that aim to help in the detection of face morphing attacks and biometric identity fraud.
A post from NIST introduces Face Analysis Technology Evaluation (FATE) MORPH 4B: Considerations for Implementing Morph Detection in Operations (NISTIR 8584), described as “a lay-language introduction” to morphs and how to handle them.
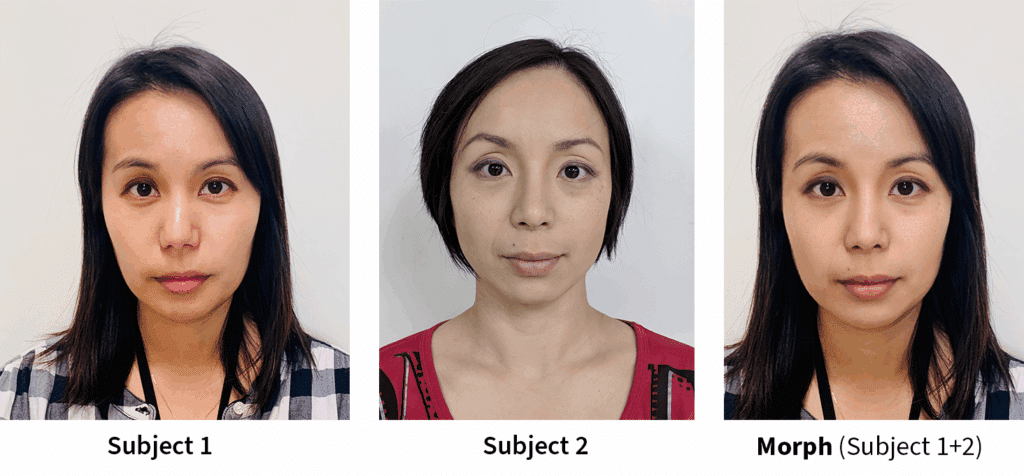
In brief, face morphing software that synthesizes photos of different faces into a single image can make it easier to bypass identity verification systems. “Morphed photos can deceive face recognition systems into falsely identifying the image as belonging to both original individuals, allowing the first individual to assume the second person’s identity and vice versa.” The best defense prevents morphs from getting into operational systems and workflows at all.
Like deepfake tools, face morphing software is easy to find and use. But, also like deepfakes, some morphs are better than others, and they differ across technologies. For detecting morphs, NIST describes two different detection situations: “In one, called single-image morph attack detection, officials possess only the questionable photo, such as processing a new application in a passport office. In the other, differential morph attack detection, they have the questionable photo along with a second image that is known to be genuine, such as a photo taken of the person at a border crossing.”
The guidelines “discuss the capabilities and limitations of detectors in both scenarios.”
NIST’s Mei Ngan, an author of the publication, says that “some modern morph detection algorithms are good enough that they could be useful in detecting morphs in real-world operational situations. Our publication is a set of recommendations that can be tailored to a specific situation.”
As such, it focuses primarily on use cases. “The bulk of the guidelines concern how one might configure morph attack detection software under different scenarios, and they suggest steps and procedures to help investigators when the detection software flags a suspicious photo.”
“What we’re trying to do is guide operational staff in determining whether there is a need for investigation and what steps that might take,” Ngan says.
Article Topics
AI fraud | biometrics | face biometrics | face morphing | morphing attack | Morphing Attack Detection (MAD) | NIST | research and development






Comments