Highly scalable biometric injection spoof attacks on the way

An executive in the biometric face verification sector may have thought he would slay when telling a FIDO Alliance conference audience about a rise in biometric injection attacks, but it was his example of how rapidly such attacks could scale that startled those seated.
Ajay Amlani, senior VP and head of the Americas for iProov, was speaking at Authenticate 2022 about the rising threat posed for biometrics industry (and potential victims) by injection attacks.
Over the last two years, Amlani said, these attacks have become a global threat.
They are easy to wage, he said, and “some scenarios are nearly impossible to detect.”
What is more, there is a “lack of standards around protecting infrastructure.”
These biometrics attacks are indirect and involve a real biometric trait that is digitally approximated. The fake is passed on to internal biometric recognition software which makes a decision based on what in reality is fraudulent data.
Injection attacks are a form of biometric presentation attack, but in the form of a bypass, which means they are beyond the scope of most PAD tests.
There are many avenues that can be exploited, but one of the more chilling is injecting deepfake video into a phone’s feed.
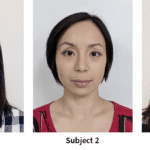
A French research paper on the topic surfaced this summer and makes clear that Amlani is not crying wolf.
“The development of remote digital identity verification solution paves the way for new attacks that are more accessible for attackers because the mobile phone is under the attacker’s control with no scrutiny from any authority,” wrote the researchers from a variety of labs in France.
“A web browser is even more vulnerable to this type of attack because a simple webcam simulation tool makes it possible to inject videos via the web browser,” they wrote.
The situation is disturbing on its face, but in the course of his brief session, Amlani talked about the unprecedented speed at which new exploits like injection attacks are being found and at the scale at which they are being unleashed.
He recalled for the audience how someone created a fake digital coupon that a fake Target.com account could use to defraud the company of three dollars on a two-dollar item.
In 32 minutes, Target lost $17 million to new accounts, making recovery unlikely. The actual total could be greater, Amlani said, if the company is forced to repay the two dollars that the fraudsters paid for the item, which was not delivered.
Almost as an aside, Amlani said the retailer’s executives initially were happy that none of the claimed items were delivered, not realizing that they nonetheless had had $17 million stolen.
They consoled themselves knowing that they at least had millions of new accounts, not realizing that most if not all of the accounts were fraudulent.
BioID also warned about injection attacks in a sponsored post for Biometric Update earlier this year.
Article Topics
Authenticate Conference | biometric liveness detection | biometrics | FIDO Alliance | fraud prevention | injection attack detection | iProov | presentation attack detection





Comments